SOLUTION BRIEF
When It Comes to a Data Breach, the Best Defense Is a Good Offense
About C² Discover
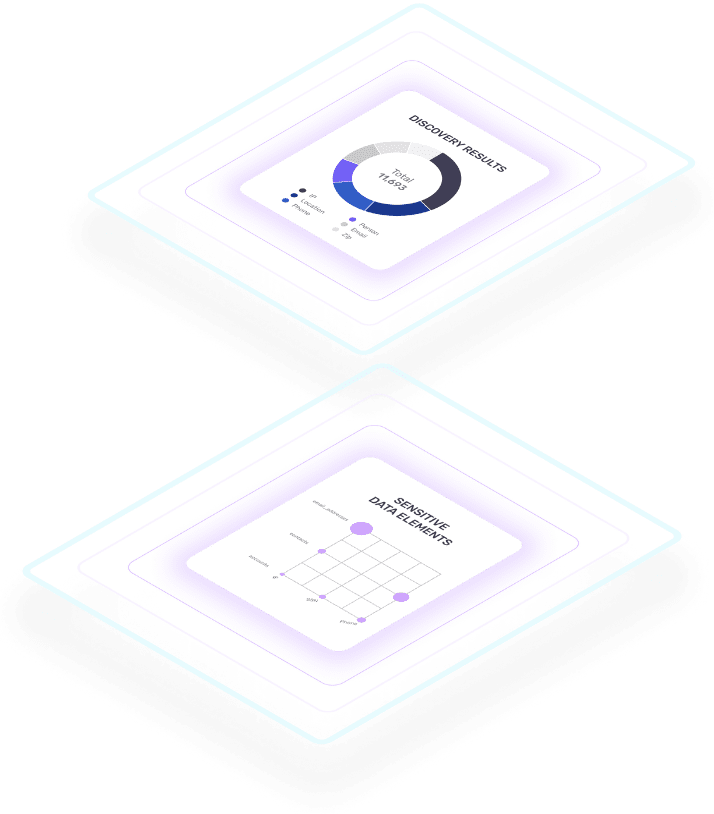
Data privacy regulations like HIPAA, CCPA, GDPR, and the Brazilian LGPD, require organizations to evolve and improve their data governance practices. The challenge is that data governance requires time, resources, and money. Initially locating sensitive data can be finding a need in the haystack, which is often the reason why companies only react when they find an audit finding. Throughout our 20 years of experience, we have assisted a variety of companies to identify sensitive data that fuels any data governance initiative. We have taken our experience with the different use cases to create a cloud-native data identification product that is cost-efficient, low-friction, and turbocharges your data privacy initiative. C² Discover combs through your cloud data files, looking for sensitive data. Avoid the fines and better understand your data with C² Discover.
Benefits
Machine Learning: Our machine learning is next generation as it differentiates between data that has a different context, or is in the wrong location, eliminating human error.
Reliability and Connectivity: C² Discover finds hidden, forgotten or lost sensitive data stored in the cloud without any manual intensive analysis.
Surgical Data Privacy: Knowing where your sensitive data is the first step to protecting it. No more time wasted figuring out where sensitive data is, now you can focus on protecting it.
AWS provides a secure foundation
Amazon Web Services (AWS) helps protect millions of active customers across the globe from threats like ransomware. These customers represent diverse industries with a range of use cases, including large enterprises, startups, educational institutions, and government organizations. Because of the scale and reach of these customers, broad visibility, and deep perspective on cloud security, which is rapidly reinvested back into its infrastructure and services.
Best practices to strengthen security
Amazon Web Services (AWS) makes it easier for you to implement security best practices with services and guidance supporting each step of the process. First, make sure to back up and restore your data. You can build and deploy highly available and resilient applications with AWS Backup, CloudEndure Discovery Recover, and Amazon S3 Glacier Vault Lock. Next, continually update and patch vulnerabilities in your systems using Amazon GuardDuty, AWS Security Hub, and AWS Systems Manager Patch Manager. It’s not enough to have an incident response plan, you also need to test it. Start with the AWS Security Incident Response Gudie, And as you are testing your response plan, be sure to also follow the guidelines for AWS Penetration Testing. Finally, make it a habit to segment your networks by isolating and protecting them with Amazon Virtual Private Cloud (Amazon VPC) and AWS Network Firewall.
Find your PII in Your Data
Enjoy a free 30-day trial of C² Discover. Gain control of your cloud data with C² Dsicover, with its modern sensitive data technology. Using next-generation machine learning and AI technology, C² Discover finds sensitive data in a wide variety of cloud data sources including RDS and MongoDB Atlas databases. C² Discover reads a variety of file types including images, S3 buckets, JSON, and more. C² Discover provides you insights into what you can store in the cloud, giving you the power to manage or govern your data as required. During this trial period, you’ll be able to connect C² Discover to your databases and scan your data as much as you want.
Resources
AWS Cloud Security: Guidance, best practices, and services for end-to-end cybersecurity
C² Data Technology: C² Data Technology has more than 20 years of experience working with Fortune 500 companies to achieve their data privacy goals.